The 30-Year Status Code That Just Became the Most Important Number in Agent Commerce
In 1992, a W3C outline for HTTP response codes defined status 402 as "PaymentRequired." The specification was simple: a server could refuse a request, tell the client what it cost, and the client would retry with a ChargeTo header authorizing the transaction. The web never implemented it. Four years later, the HTTP/1.0 RFC formally reserved 402 "for future use." Then RFC 7231 in 2014 did the same thing. For thirty years, 402 sat in the spec like an empty lot in a booming neighborhood, everyone agreeing it was valuable, nobody building on it.
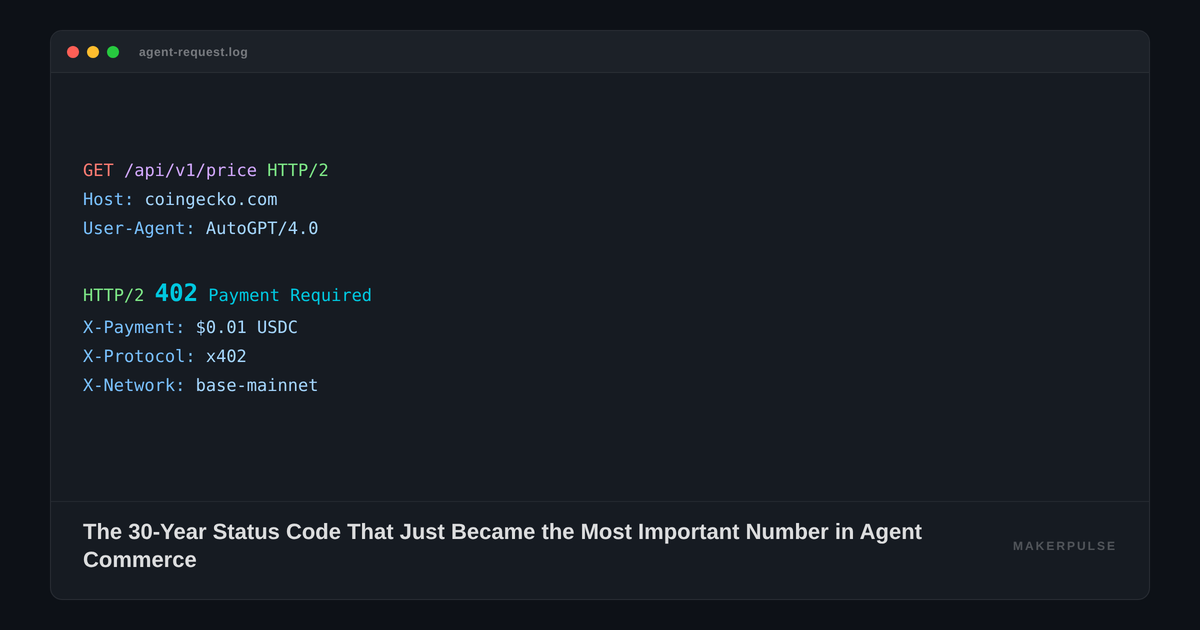
On February 11, 2026, Stripe's product lead Jeff Weinstein posted that the company was previewing machine payments built on x402, a protocol that finally puts that empty lot to work. CoinGecko activated the first major production endpoint at $0.01 USDC per API call. And Cloudflare quietly positioned itself as the cryptographic checkpoint that every agent must pass before completing a Visa or Mastercard transaction.
The open protocol crowd got its open protocol. But the routing question, the one that determines who actually captures value, is already settled. And the answer isn't Coinbase.
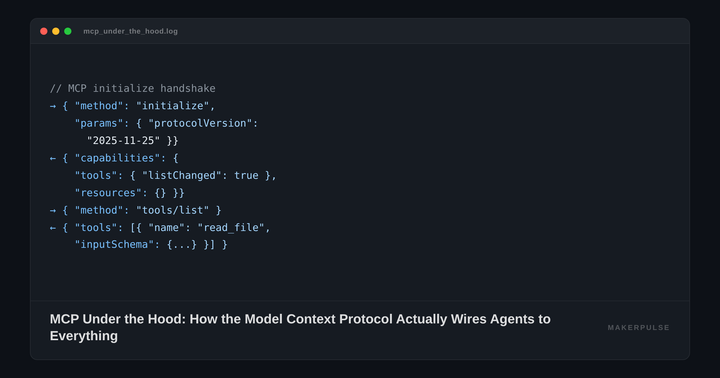
What the Handshake Actually Looks Like
The x402 flow is elegant in the way that good protocol design always is. Your agent sends a GET request to, say, CoinGecko's /x402/simple/price endpoint. The server responds with HTTP 402 and a set of payment terms: $0.01 USDC on Base. The x402 client library detects the 402 response, signs a USDC authorization with your wallet, and retries the request with the payment signature attached. The server verifies the signature, settles the transaction onchain, and returns the data. No API key registration. No OAuth dance. No billing portal. Just an HTTP request that costs a penny.
Coinbase built this. Erik Reppel and a team at the Coinbase Developer Platform authored the x402 whitepaper, and the protocol is genuinely open source and chain-agnostic. It works on Base and Solana today. The protocol saw a spike of over 492% week-over-week in October 2025, reaching roughly 156,000 weekly transactions at its peak, though analysts noted much of that volume was driven by speculative token activity rather than genuine agent commerce. Google collaborated with Coinbase, the Ethereum Foundation, and MetaMask to build an x402 extension for its Agent Payments Protocol (AP2). A separate but compatible protocol, Google's Universal Commerce Protocol (UCP), now powers agentic checkout through Etsy and Wayfair in Google's AI Mode.
Weinstein framed Stripe's move in practical terms: current payment systems are designed for humans and don't work for automated software. Agents need microtransactions, 24/7 global rails, HTTP-native integration, low latency, and finality guarantees. Stripe's implementation maps x402 onto its existing PaymentIntents API. A merchant creates a standard Payment Intent. Stripe generates a unique wallet address. The agent sends USDC to that address, and the payment shows up in the merchant's Stripe dashboard, with webhooks and reporting working through familiar Stripe infrastructure. Stripe also released an open-source CLI tool called purl and sample code in Python and Node.js so developers can test machine payments immediately.
This is the part where the crypto-native crowd celebrates. An open payment standard, stablecoin settlement, no intermediary rent-seeking. Except that's not what's actually happening.
Who's Standing at the Door
Here's where I think most coverage of x402 misses the point. The protocol is open. The authentication layer sitting on top of it is not.
Cloudflare processes more than 20% of all global internet request traffic. If your agent is calling an API, there's a one-in-five chance the request routes through Cloudflare's network before it touches the origin server. And Cloudflare has partnered with both Visa (through the Trusted Agent Protocol) and Mastercard (through Agent Pay) to serve as the cryptographic verification layer for agentic commerce.
When an agent makes a purchase request to a merchant running behind Cloudflare, seven checks execute before the x402 payment handshake even begins. Rohin Lohe and Will Allen described the full sequence on Cloudflare's engineering blog. First, Cloudflare confirms the presence of Signature-Input and Signature headers in the request. Second, it extracts the keyid from the signature input and fetches the agent's public key from a directory (caching it for subsequent requests). Third, it validates that the current time falls between the created and expires timestamps in the signature. Fourth, it checks nonce uniqueness against a cache, rejecting any reused or expired signatures to prevent replay attacks. Fifth, it validates the tag field matches the protocol context: agent-browser-auth for browsing, agent-payer-auth for payments. Sixth, it reconstructs the canonical signature base using components from the Signature-Input header per RFC 9421. Seventh, it performs ed25519 cryptographic signature verification using the public key.
Fail any one of those seven checks, and your agent never reaches the merchant. It doesn't matter that x402 is open. It doesn't matter that your USDC is sitting right there. The gatekeeper said no.
This isn't theoretical. Visa's Trusted Agent Protocol, introduced in October 2025 with more than 10 partners, has already completed hundreds of agent-initiated transactions in production. Visa SVP Rubail Birwadker stated it plainly: "In 2026, AI agents won't just assist your shopping, they will complete your purchases." Mastercard's Agent Pay requires agents to register with Mastercard's network using cryptographic tokens. Only verified agents can initiate transactions. Both protocols lean on Cloudflare's Web Bot Auth implementation as the verification foundation, built on the IETF RFC 9421 standard.
The architecture, then, looks like this: Coinbase defines the payment protocol. Stripe handles settlement. Visa and Mastercard define the trust framework. And Cloudflare sits physically between the agent and the merchant, running cryptographic verification on every single request. Open protocol, private gatekeeper. This is "who controls the routing?" in the most literal possible sense.
The Practitioner's Problem
If you're building agents that consume external services, this matters right now, not in some abstract future. Let me walk through what changes.
Today, your agent calls an API using an API key. You registered for that key, maybe paid for a subscription tier, and your agent includes it in the request header. The failure modes are well understood: rate limits, expired keys, insufficient plan. Tomorrow, your agent will encounter x402-enabled endpoints that don't require API keys at all, just USDC. (This shift is closely tied to a broader infrastructure push: WebMCP is simultaneously making websites readable to agents, so that the agents doing the transacting can also navigate the services they're paying for.) That sounds simpler until you realize the endpoint sits behind Cloudflare, and Cloudflare requires your agent to present a valid HTTP Message Signature before the 402 handshake even starts.
This means your agent needs a cryptographic identity. Not an API key. Not an OAuth token. A public/private key pair where the public key is registered in a directory that Cloudflare can query. Your agent needs to construct RFC 9421-compliant HTTP Message Signatures on every request, including authority, path, creation timestamp, expiration timestamp, key identifier, algorithm specification, nonce, and a tag indicating whether it's browsing or buying. If your agent framework doesn't support this, your agent can't transact.
Consider a concrete scenario. You're running an autonomous research agent that aggregates crypto market data from multiple sources. CoinGecko now offers x402 endpoints at $0.01 per request. Your agent can pay for data on demand, no subscription needed. But CoinGecko runs behind Cloudflare. Your agent needs to pass all seven verification checks, sign x402 payment authorizations, and manage nonce state to prevent replay rejections. That's three layers of cryptographic plumbing (identity, authentication, payment) that didn't exist in the API-key world.
The good news is that Stripe's integration simplifies the payment layer. If you're already on Stripe, you can use their PaymentIntents API and let them handle the USDC settlement. The bad news is that the authentication layer is Cloudflare's, and Cloudflare plans to bake this into their Agent SDK. If you're building on Cloudflare Workers, this probably just works. If you're not, you're implementing RFC 9421 yourself or waiting for someone to ship a library. This authentication requirement is worth flagging if your team is evaluating enterprise agent platforms like OpenAI's Frontier, which abstracts some infrastructure concerns but won't handle Cloudflare's seven-check identity layer for you.
Google's protocols add another wrinkle. Google extended its Agent Payments Protocol (AP2) with an x402 integration built in collaboration with Coinbase, the Ethereum Foundation, and MetaMask. The Universal Commerce Protocol (UCP), a separate but AP2-compatible standard, already lets U.S. shoppers buy from Etsy and Wayfair through Google's AI Mode. If your agents operate inside Google's stack, UCP handles the commerce layer with AP2 providing payment plumbing underneath. If they don't, you're stitching it together yourself.
The fragmentation risk is real. Three major payment trust frameworks (Visa's Trusted Agent Protocol, Mastercard's Agent Pay, Google's AP2), one underlying payment protocol (x402), and one dominant authentication gateway (Cloudflare). Your agent might need to support multiple trust frameworks depending on which merchants it transacts with.
The HN Crowd Gets It Half Right
The Hacker News discussion around x402 and agent payments has been instructive. User wslh raised the sharpest objection: "If smart contracts were the precedent for handling digital money automatically, and are deterministic yet notoriously difficult to secure, then agents, which are even less predictable, could prove to be just as bad, or worse." This is correct as far as it goes, but it targets the wrong layer. User paool countered that the protocol itself is straightforward; the security risk lies in "whether an agent is unable to call a tool to perform it in the first place," not in the payment mechanism.
My read is that both are missing the structural question. The security of x402 transactions isn't primarily a protocol problem or an agent-capability problem. It's a gatekeeping problem. Cloudflare's seven-check authentication sequence is explicitly designed to distinguish "legitimate AI shopping agents from malicious bots." Who decides what's legitimate? Cloudflare does, in consultation with Visa and Mastercard. The protocol may be open, but the definition of a trusted agent is private.
User mike_hearn referenced a decade-old talk he gave about autonomous agents using Bitcoin for frictionless commerce, saying the vision seemed far-fetched at the time. He's right that the vision is finally arriving. But the version arriving looks nothing like the permissionless ideal that Bitcoin envisioned. It looks like Cloudflare checking your agent's papers at the border.
My Position
Here's what I think happens over the next 18 months. x402 becomes the default payment protocol for agent-to-service transactions. Stripe's integration ensures that every merchant already on Stripe can accept agent payments with minimal code changes. CoinGecko is the first of dozens of data providers that will flip on x402 endpoints. The penny-per-request model kills the API subscription as the default pricing tier for machine consumers — a disruption that extends well beyond data APIs to the entire layer of SaaS tools that charge for pattern-matching work agents can now do directly.
But Cloudflare becomes the chokepoint. Not because they're evil, but because they're positioned. Twenty percent of internet traffic already routes through their network. Both Visa and Mastercard chose Cloudflare as their verification partner. As x402 endpoints proliferate, the percentage of agent-to-service traffic that passes through Cloudflare's authentication layer will only grow. Cloudflare's Agent SDK will become the de facto standard for building agents that can transact, the same way their Workers platform became the de facto standard for edge compute.
The strategic bet I'd make: within two years, the most common failure mode for autonomous agents won't be hallucination or task decomposition. It will be authentication failure. Your agent will be smart enough, funded enough, and correctly instructed, but it won't be able to buy the data it needs because it can't pass Cloudflare's seven checks. The open protocol will work perfectly. The private gatekeeper will be the bottleneck.
For practitioners, the implication is immediate. If you're building agents that need to transact, start implementing RFC 9421 HTTP Message Signatures now. Get your agent's cryptographic identity registered. Build against Stripe's x402 preview. And pay very close attention to Cloudflare's Agent SDK roadmap, because that SDK is about to become the most important dependency in your agent's stack. Not because it handles payments. Because it handles permission.